Follow this tutorial to start setting up a ShadowsocksR proxy server and enjoying freedom outside the wall!
Server-side Setup
Prepare a server
I would recommend DigitalOcean and Vultr, both of which offer various plans for virtual private servers (VPS). DigitalOcean provides $100 credits for new users, while Vultr provides $25 credits for new users. Students with a valid .edu email address can sign up for GitHub Student Developer Pack and get an extra $50 credits on DigitalOcean. Google Cloud and Microsoft Azure, at the same time, also provide free credits for trial, but they can exhaust faster. These free credits usually last for only one year, so you should take full advantage of them before they expire. If you have access to a dedicated server, keep in mind that you should have full access to it.
I will deploy a Vultr Cloud Compute (VC2) server with Ubuntu 18.04 in this tutorial.

Install ShadowsocksR Proxy Server
In this tutorial, we will use a script developed by Toyo to help us install the proxy server. This script installs and runs the proxy server in the MudbJSON mode so that the we can manage each user of the proxy server separately. For those who are interested in the technical details of this script, please refer to 『原创』ShadowsocksR MudbJSON模式多用户一键脚本 支持流量限制等 (Chinese).
Thanks to the script, the installation can be extremely easy. First, download and run the script.
1 | wget -N --no-check-certificate https://raw.githubusercontent.com/ToyoDAdoubi/doubi/master/ssrmu.sh && chmod +x ssrmu.sh && ./ssrmu.sh |

Enter 1 to start the installation of ShadowsocksR proxy server.

First, hit Enter to let the script automatically detect the IP address of the server. Then enter user name, port number and password for the first user.
The username and password should only contain ASCII characters. The port entered here should not have conflict with the ports which the server is using or the server system reserves.

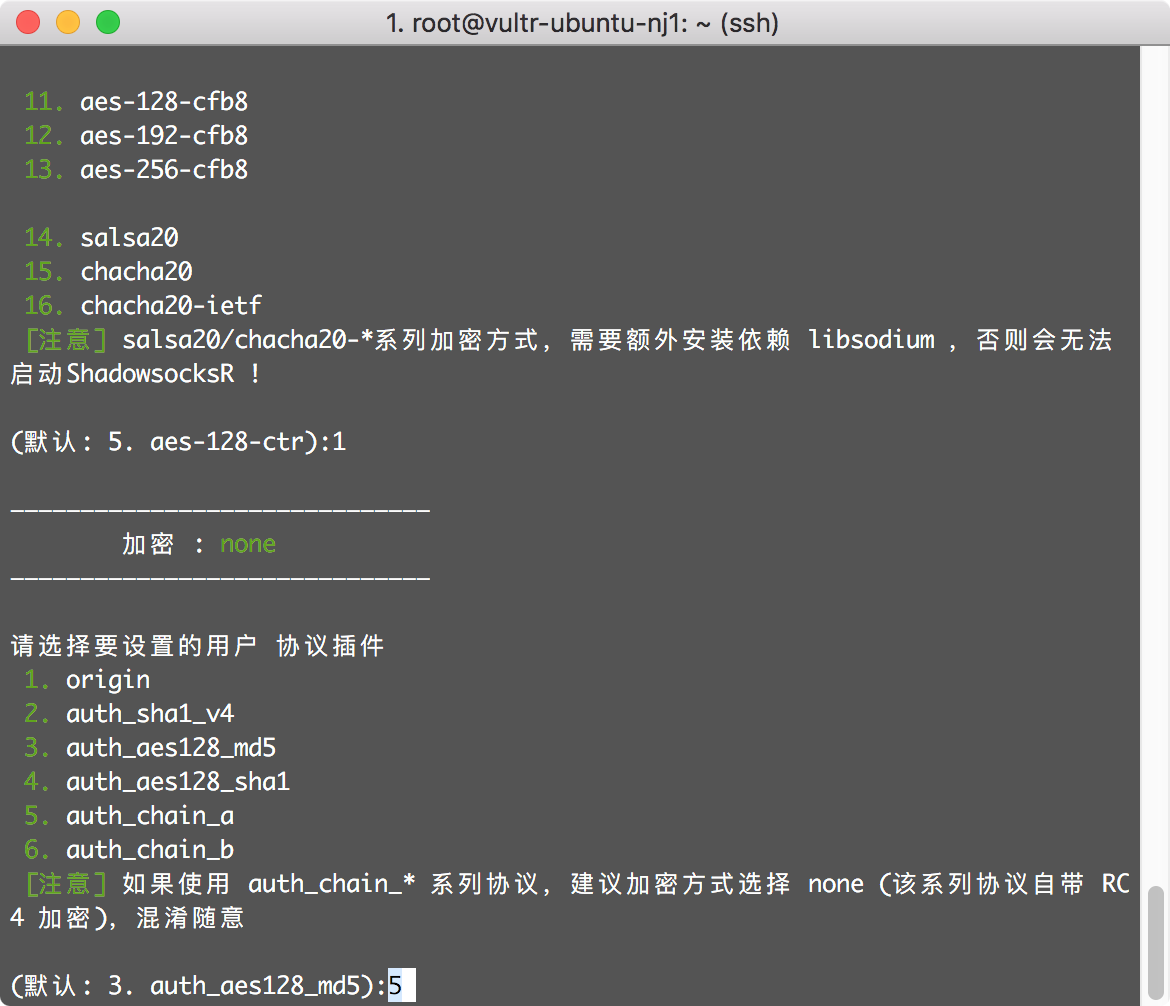
For the encryption method, select “none” (i.e. enter 1) since I will use “auth_chain_a” protocol later.

Now select “auth_chain_a” protocol (i.e. enter 5) because it is safer.
For more information about “auth_chain_a” protocol, please refer to 协议auth_chain_a是啥 (Chinese) or https://github.com/shadowsocksr-backup/shadowsocks-rss/blob/master/doc/auth_chain_a.md (English). You might also use “auth_chain_b” protocol, but it has not been widely supported on the iOS devices yet.
Use the default setting for obfuscation (i.e. enter 5) with no compatibility with Shadowsocks (i.e. enter n). Original Shadowsocks proxy is no longer safe, so it is not necessary to make the server compatible with Shadowsocks.
For more technical information about encryption method, protocol and obfuscation in ShadowsocksR, please refer to ShadowsocksR 协议插件文档 (Chinese).

Use the default settings for all remaining parameters unless you want to limit the device number, the network speed, the traffic and/or the ports of the current user.

Finally, the script shows that the proxy server is installed successfully, and the first user is configured. Write down the ShadowsocksR URL starting with ssr:// or the QR code URL so that we can add this configuration to the clients later.

If you want to add another user, just run the script again by ./ssrmu.sh, choose 7 and follow the exact same instruction.
In theory, we should boost our proxy server’s TCP connection. The good news is that Ubuntu 18.04 enables Google BBR by default, so we do not need to take any further action. If you use other versions or systems and need to enable it manually, please follow this tutorial: Centos/Ubuntu/Debian BBR加速一键安装包 (Chinese).
Debian 9 users can use the following commands to enable Google BBR:
2
3
echo "net.ipv4.tcp_congestion_control=bbr" >> /etc/sysctl.conf
sysctl -pFor more information, please check out this post: Debian 9快速开启Google BBR的方法,实现高效单边加速.
And don’t forget to set firewall rules for the server! DigitalOcean and Vultr provide graphical interface inside their consoles so that users can set up firewalls in clicks.
Client-side Setup
I would recommend the following client-side applications:
- macOS: ShadowsocksX-NG
- Linux: electron-ssr
- Windows: ShadowsocksR C#
- iOS: Potatso Lite
- Android: ShadowsocksR for Android
Reference
- Toyo, “『原创』ShadowsocksR MudbJSON模式多用户一键脚本 支持流量限制等,” 逗比根据地. [Online]. Available: https://toyodadoubi.github.io/z2a4lk3l-2.html.